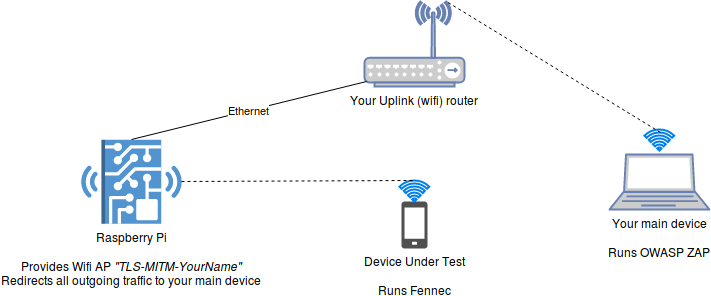
How to Build a Pumpkin Pi — The Rogue AP & MITM Framework That Fits in Your Pocket « Null Byte :: WonderHowTo
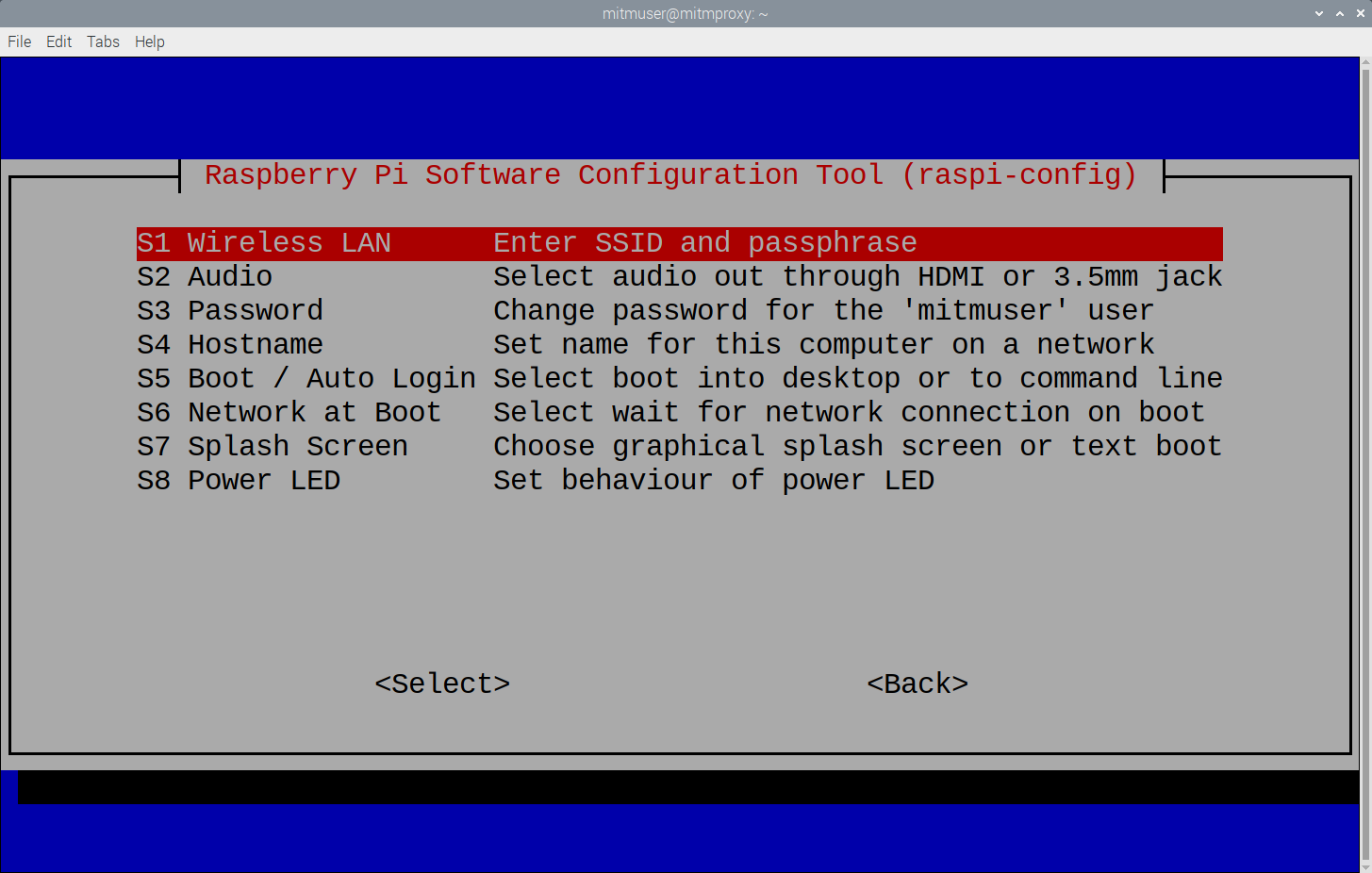
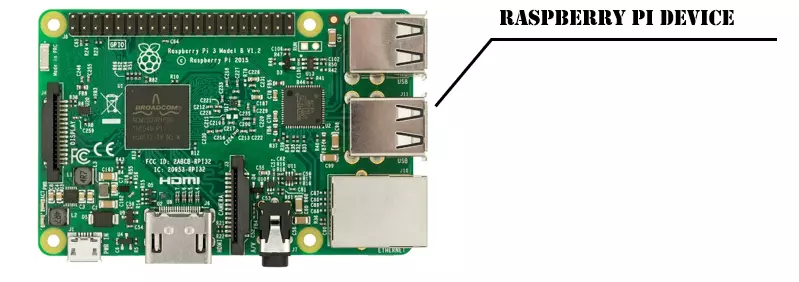
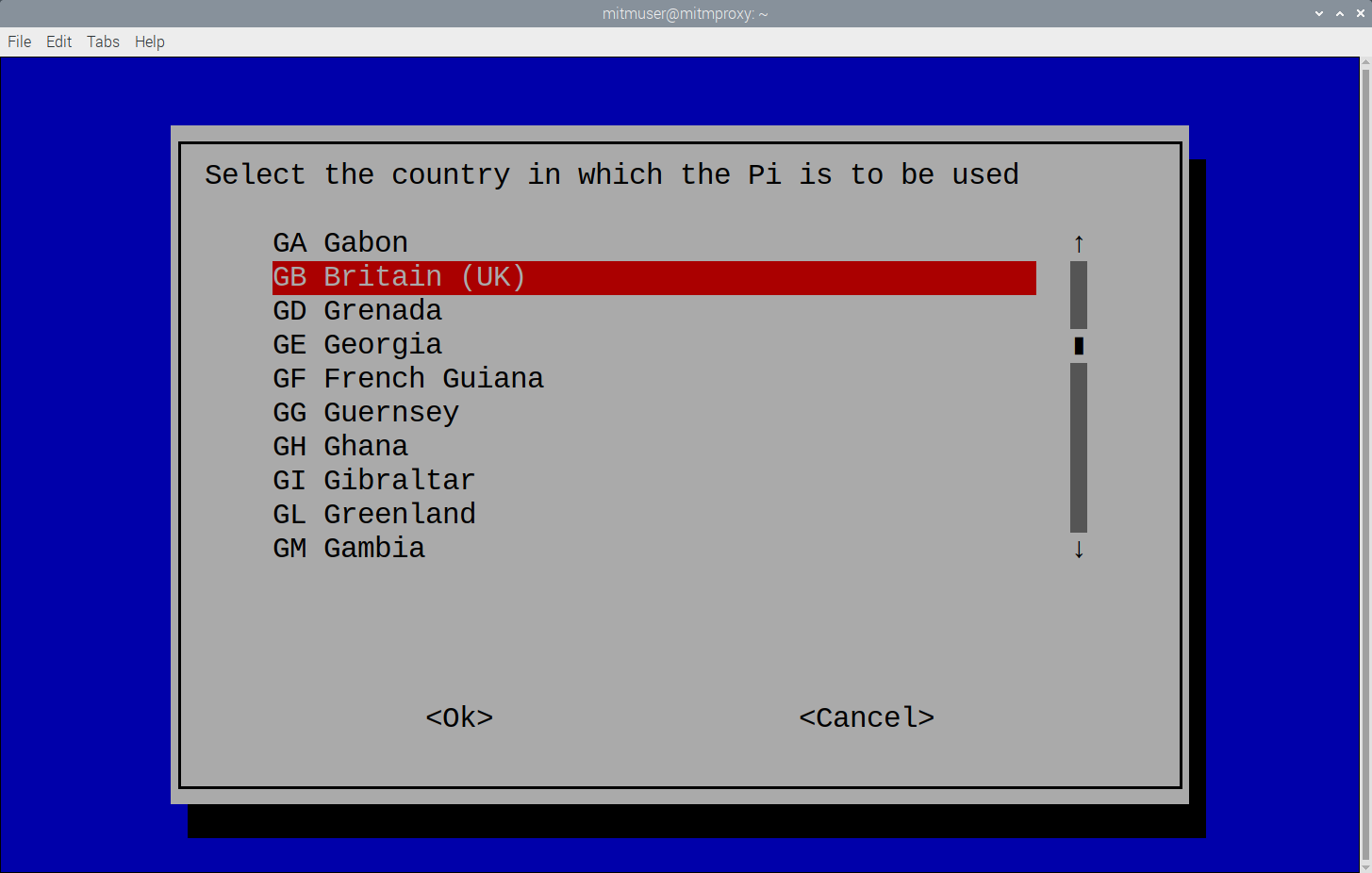
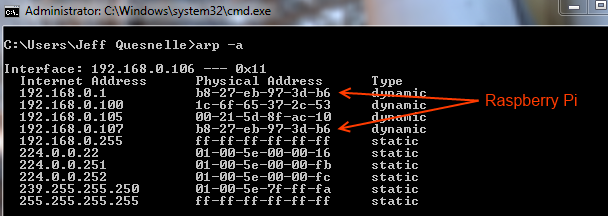
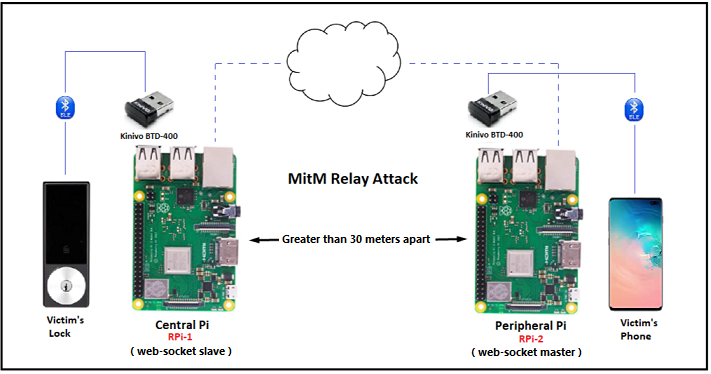
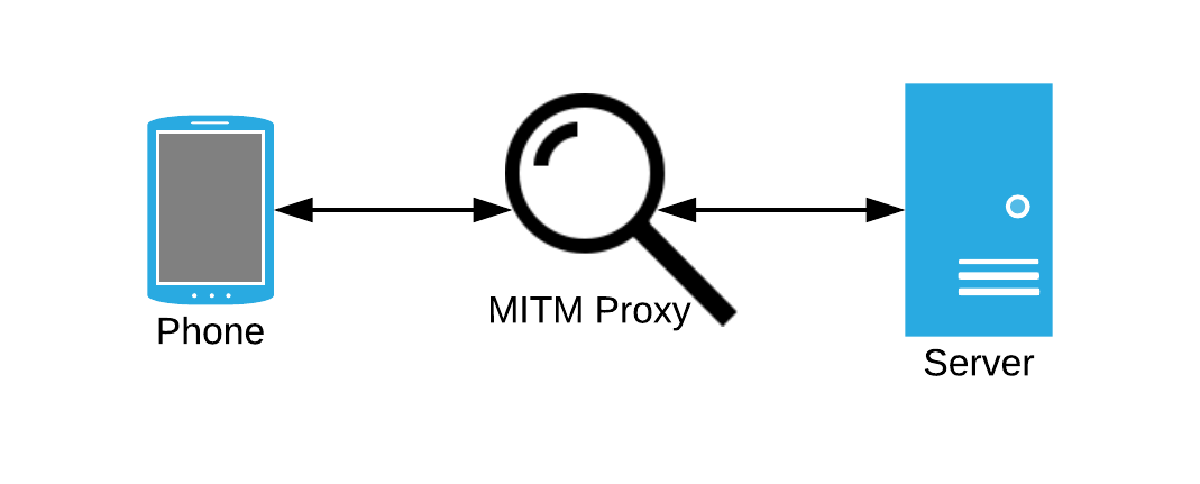
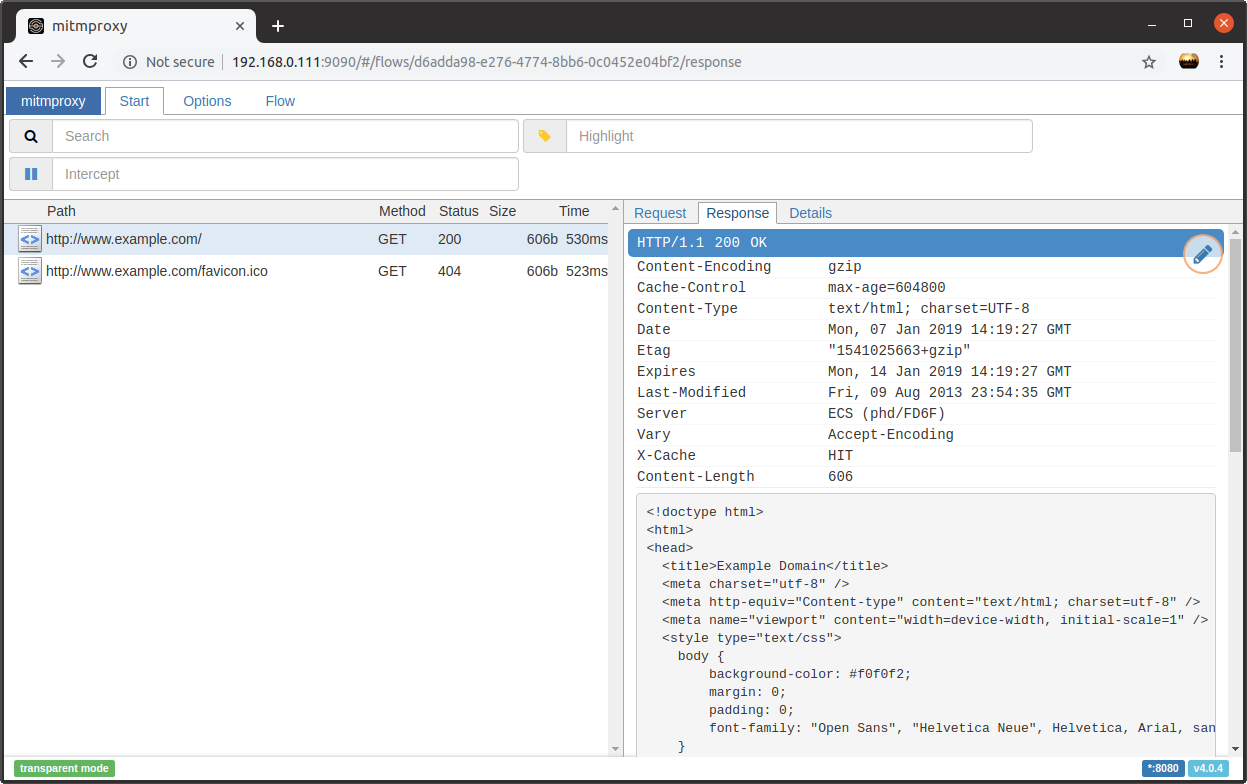
Phase I Man in the Middle Attack with a Raspberry Pi The raspberry pi is a very inexpensive and useful device for many things. O

RaspberryPi – How to solve the SSH warning: WARNING: REMOTE HOST IDENTIFICATION HAS CHANGED! – El Bruno